In our current digital age, each click, search, and internet interaction we partake in creates a digital trail, casting the concept of ‘privacy’ as something elusive. The web, with its extensive networks interconnected, has revolutionized the way we connect, disseminate information, and fundamentally experience our daily lives.
Yet, in this digital realm, shadows linger—shadows of our past searches, our forgotten sign-ups, and our seemingly inconsequential digital footprints. These remnants, if not addressed, can paint a comprehensive picture of who we are, what we like, where we go, and even what we might do next.
The title How To Delete Yourself From The Internet might sound like a drastic measure to some, but in reality, it’s a call to reclaim control over one’s digital identity.
Table of Contents
How to delete yourself from the internet
Step 1: Preliminary Requirements Go through each email you can think of that you’ve used in the past 10 years. You’ll want to recover them if you’ve lost access, so that you can access other websites you may have signed up to using them.
Step 2: Deleting old accounts from forgotten services Use the search function on your e-mail and look for phrases such as “Sign up” or “Welcome” Recover account and login into each service that pops up (that you received a sign-up email) from
Step 2b: Now look around the service for a delete account function, google around by searching “”delete account” + “<service>” If there isn’t one, google or look around for a support e-mail to request for them to delete your account.
Step 2c: For some services, you may want to purge all content and messages before you delete the account, as the account may be archived and a hacker or external entity may access this information at a later date. That’s something to bare in mind.

Step 3: Checking if your information has been compromised already. Now you should have a list of all your usernames and all the services, ranging from streaming services to e-mails. You need to use something called boolean searches to properly use Google to locate this info
Step 3b: I’ll be using “s to denote normal quotations, as you will need to use the normal “” signs to perform these searches. You need to google your account name “<account_name>” Sometimes maybe your account name + password like so: “<account>” + “<password>”
Step 3c: You should see possibly pastebin links or underground databases publicly accessible on the internet, or possibly leaked private information. This is normal. It happens to a lot of services. Note down what passwords/information was compromised.
Step 3d: Some database leaks are a bit more private and are still being shared/sold in private circles, but you can use this website: https://haveibeenpwned.com To check if you’ve been compromised, so you can change your live information to be different..
Step 4: Removing yourself from Google. So now you’ve deleted your Facebook accounts, but when you google your name and location using boolean searches, there is cached information/links about yourself. There is a solution for that, called the Google Console.
Step 4b: You can use Google Console at: https://google.com/webmasters/tools/removals… You can request for them to delete/update their search engine (which usually takes months organically) to remove those cached results if you provide a link to each. Go through various google searches and do this
Step 5: Protecting yourself against Google legally tracking you (for the most part). You should be disallowing Google to legally touch any of your data Here you can go through each of Google’s services: https://myactivity.google.com/activitycontrols
Step 5b: Protecting yourself against other services Any other services you wish to use, you need to strip down the privacy settings to the absolute core. If you want to use Facebook, make sure you make it almost entirely private, so people can’t access private photos.
Step 6: Deleting old e-mails Now you’ve just access to your old e-mails, it’s time to delete them too. Delete any e-mails you no longer need access to DO NOT DELETE E-MAILS YOU MAY NEED IN THE FUTURE. If you do need them, change security questions and password.
Step 7: Securing accounts You should be REGULARLY changing your passwords on services every 6 months Why? Because new hackers gain access to new databases daily, and they’ll start using that information to brute force, or in the future, to personally attack you.
Step 7b: Do NOT use any passwords similar to each other. Hackers are smart. Especially when it’s a personal attack. They will easily combine your old passwords with your home address, or date of birth to accomplish finding your password to something they need.
Once they are in, some services will give them access to EVERYTHING and it’s damn near impossible to get them out after they are in. Good news is a lot of services are updating this, so that you can only have one session active at once. Before you never knew who was in.

Step 8: PROTECTING your internet connection. You should be using a VPN when using the internet. DO NOT use a VPN when dealing with banking services or anything confidential, but do use it when publicly surfing the internet. Using DuckDuckGo in combination with this will help
Step 8b: Using a VPN that has no logs. You need to make sure your VPN has had a PUBLIC audit to ensure that it has NO LOGS. this means that it has no record of what you have used their internet connection for. And when you use a VPN, it’s hard for your ISP to know either.
Step 9: USING Burner accounts You should be using burner accounts on known intrusive services such as Google by using a fake name and information. This is LEGAL and you should do it to avoid having your information data mined across services.
Step 10: REGULARLY deleting your internet content. You should be regularly deleting your tweets and old photos. This data can be used against you to cross-reference your accounts and find more personal information. Hackers will find a target and analyze them for months.
Step 10b: Hackers will use your old internet information to do some of this analyzing in retrospect to piece together who your social circle is to find a vulnerability. Anyone can be attacked. You just haven’t been a target yet. Defend yourself through prevention.
Step 10c: Don’t believe me? https://theverge.com/2019/10/11/20910551/stalker-attacked-pop-idol-reflection-pupils-selfies-videos-photos-google-street-view-japan… This is nothing. Very simple with the tools EVERYONE has access to today.
Step 11: Basically all “background check” websites have a a way to opt out. A basic Google search for that company will give you the link. This is something that needs to be revisited as they aggregate data from the original sources like YOUR VOTING RECORDS AND USPS.
Quick update| How To Delete Yourself From The Internet
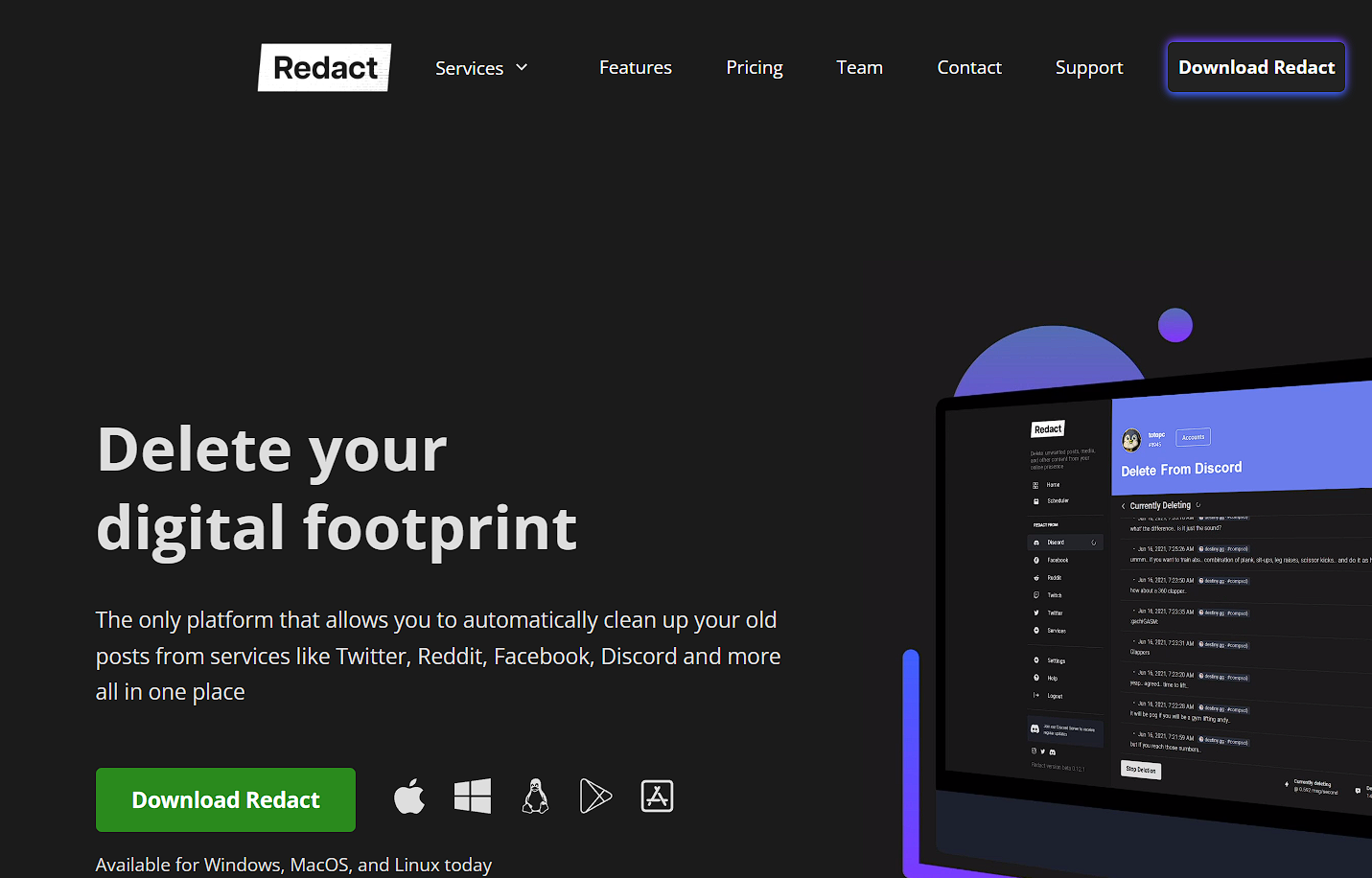
Just discovered this free tool which automates deleting your content from Twitter, Reddit, Discord and dozens of other services automatically. This saves you a lot of time for everyone saying this is a lot of work.
Conclusion
In an era where our digital selves are as prominent as our real-world personas, the steps outlined in this guide are not mere suggestions; they are necessities. The internet, while a marvel of modern technology, also harbors risks that can compromise our very identity. By taking control, by actively choosing what remains online and what gets erased, we not only protect ourselves but also set a precedent for future generations.
Through the journey of this guide, we’ve not only learned the importance of erasing our past digital footprints but also the significance of treading cautiously in the future. Each step, each action we take towards digital privacy, is a testament to our understanding of the evolving cyber landscape. It’s an assertion of our right to exist online on our own terms.
Moreover, knowledge is most potent when shared. As you now possess the tools and understanding to safeguard your digital identity, it becomes a responsibility to educate others. Spread the word, share this guide, and let’s collectively create an internet that respects privacy, autonomy, and individuality.
In conclusion, How to Delete Yourself From The Internet is more than a technical process; it’s a statement, a commitment to one’s digital well-being. As we continue to evolve and adapt in this digital age, let’s ensure that our digital footprints are a reflection of our conscious choices and not inadvertent oversights.
Are you ready to be the change and lead the way in digital privacy?
- Amazon Email Phishing: How to Identify and Avoid Scams - May 11, 2025
- Malwarebytes vs McAfee: Decoding the Ultimate Antivirus Battle - May 11, 2025
- Best Antivirus for Windows 10: Expert Recommendations for 2023 - May 11, 2025